According to the CIS, the controls are “a prioritized set of actions that collectively form a defense-in-depth set of best practices that mitigate the most common attacks against systems and networks.” Overall, there are 20 controls. Each control has specific, actionable sub-controls. Here’s what they look like (The controls in v7.1 are the same as in v7.):
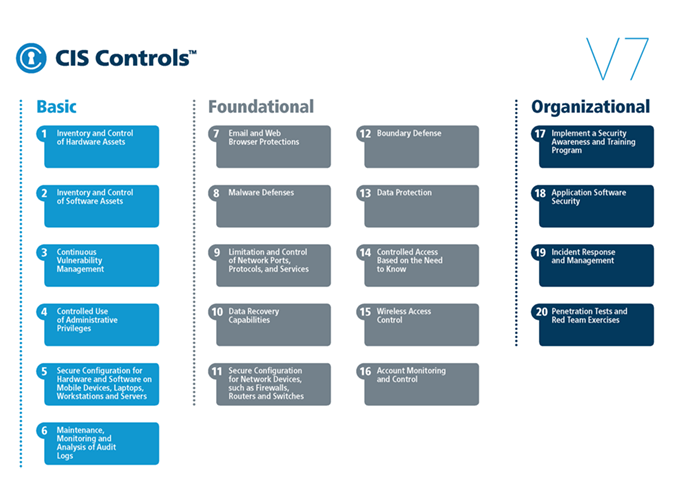
Categories of Controls
From early on, the CIS controls were organized into the three categories: basic, foundational and organizational. The idea was always to apply the basic controls first. They were judged to be essential to any security system.
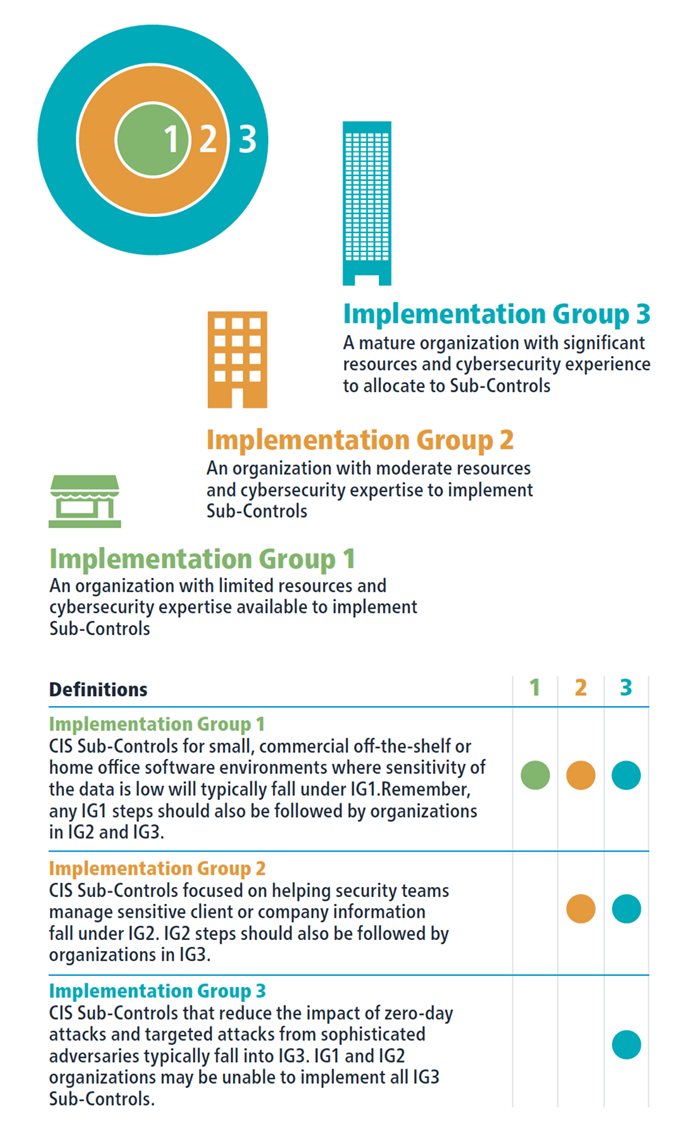
It turned out that, even in the basic controls, applying them effectively depends on an organization’s resources: What IT personnel it have? How trained are they in security practices? How much time and money can be devoted to security? Version 7.1 therefore has added the new concept of Implementation Groups (IGs). It sorts organizations into three types of groups, based on their resources.
Where Do You Fit?
We suspect that most, but not all, of CGNET’s clients fall into Implementation Group 2. According to the CIS, “An IG2 organization employs individuals responsible for managing and protecting IT infrastructure. These organizations support multiple departments with differing risk profiles based on job function and mission. Small organizational units may have regulatory compliance burdens. IG2 organizations often store and process sensitive client or company information and can withstand short interruptions of service. A major concern is loss of public confidence if a breach occurs. Sub-Controls selected for IG2 help security teams cope with increased operational complexity. Some Sub-Controls will depend on enterprise-grade technology and specialized expertise to properly install and configure.”
The idea is that an organization in IG2 should implement the sub-controls in IG1 first. Only then should it go on to add the ones for IG2. After that is done, they can consider ones in IG3. This provides a very simple way to set an agenda for implementing security controls over time.
The CIS does realize that organizations differ in other ways: There is no “one size fits all” method for security planning. The best method involves doing a risk assessment and then selecting controls. The CIS has, in fact, published a risk assessment method to use with its controls. By combining the insights of the risk assessment with the implementation group ideas, however, the project becomes achievable. Nobody needs to be overwhelmed when looking at the whole bunch of controls.
You can download the controls at https://www.cisecurity.org/controls/ and see for yourself.





0 Comments