You may have heard of QR code phishing – cutely nicknamed “quishing” to fit right in with its other phishing counterparts, like smishing (SMS phishing) and vishing (voicemail phishing). This is the latest method used by hackers to steal your credentials by weaponizing QR codes. Unfortunately, security firms have seen a huge jump in this type of phishing recently, with C-level staff targeted the most.
How does quishing work?
Essentially, scammers set up QR codes that direct unsuspecting users to malicious sites. Here are their main techniques:
Tactic 1: The Fear Factor
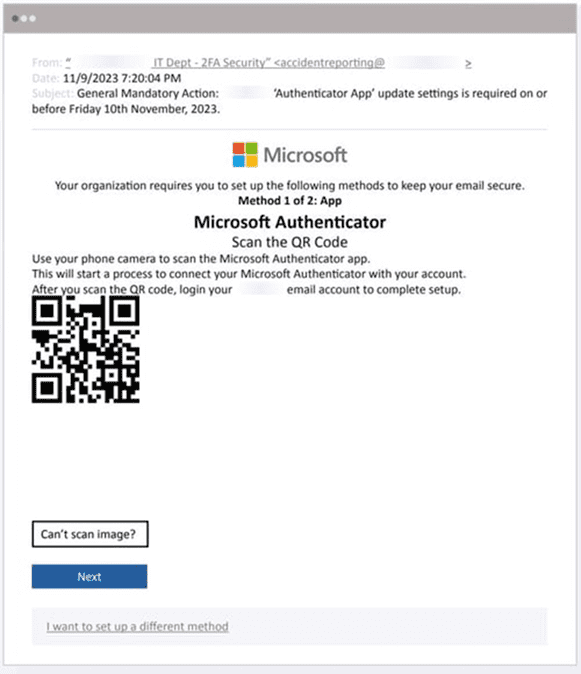
Much like traditional phishing methods, with QR code phishing the bad guys use a sense of urgency and fear to get their targets to act quickly, without thinking through their behavior. They send their targets an email appearing to come from a legitimate sender and encourage them to scan the embedded QR-code image…or else there will be some negative impact. The fake QR code then takes them to another site that – while once again looks legitimate and official – is the scammer’s own site requesting passwords, bank account information, and so on.
Tactic 2: Impersonation
This happens in a couple of ways: The quishing email mimics the branding of a known, legitimate organization. Or the hacker has already compromised an email account belonging to an organization and can then send a phony message from what is actually a legitimate domain. According to one security study, over the past year, 56% of such emails impersonated Microsoft pretended to require multifactor authentication resets or enablement. Another 18% during that 12-month period impersonated online banking pages.
Tactic 3: Hide and Sneak
In 12% of the QR code phishing incidents over the past year, the code was hidden inside an embedded PDF, JPEG or PNG file, instead of being part of the actual body of the message. This was done to bypass email filters that might otherwise flag the message as suspicious. The image would contain both the QR code and text instructing the recipient to scan it with a mobile device. While you may be thinking, what if the recipient were already ON their mobile device when reading the email message? Well, some scammers have already thought of that. By adding a “Can’t scan the code? Click here instead” type instruction, they’ve added an air of legitimacy to the instructions, and have us doing all kinds of things (scanning, clicking links) we have been taught to never do!
Unfortunately, this method is very typical of large-scale, credential-harvesting campaigns, and employees should be warned.
Some not-so-fun facts & stats
A threat report conducted for the first part of this year revealed the following:
- 3% of QR code attacks involved credential phishing
- 27% of attacks impersonated multi-factor authentication (MFA) notifications
- 21% of attacks sent targets fake notifications of a shared document
- SMBs (organizations with up to 500 employees) are 19 times more likely to receive a QR code phishing attack than the largest enterprises with more than 50,000 employees.
- 42% of targets were C- level employees. (No one is immune, especially not your CEO!)
Defend against QR code phishing
Unfortunately, research shows that a large percentage of users receiving a QR code will follow it without any hesitation. This is where security training becomes essential. All staff – from interns to C-level leaders – need to know that a legitimate business would never require anyone to use a secondary device to scan a QR code in an email. You should also educate staff on all the signs of phishing (quishing/smishing/vishing) and conduct regular phishing simulation exercises. Encourage them to spend more time analyzing their incoming messages for obvious signs before taking any action. Fortunately, as of now simply following a QR code rarely results in the silent installation of malware. Since a QR code usually takes the user to a landing page, thorough training will remind the user to evaluate the page for any signs of phishing (typo in URL, poor grammar, and so on).
IT administrators can also act by setting up email inbox rules that highlight messages from external senders, to help flag potentially malicious emails to employees. Also, admins should consider blocking or flagging emails that contain no body text.
With training and a bit of administrative action, QR code phishing can become a far less formidable adversary.




0 Comments