First, I hope you and your loved ones are safe, washing your hands and physically isolating as much as possible. Second, I hope your users are finding their footing as they work remotely, and that the days of drop-shipping monitors and cables to people’s houses is behind you. Now, let’s talk about steps you can take to improve remote working security.
The Coronavirus Pandemic Has Been a Gift to Hackers
I came across a chart from Statista, based on a Trend Micro report, that showed how hackers have been capitalizing on the coronavirus pandemic to conduct phishing and other attacks. You can read the Statista article here.
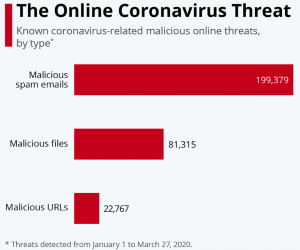
Hackers sent close to 200,000 phishing emails in a three-month period. We’ve seen this pattern before, where hackers have attempted to exploit major events (earthquakes, fires, etc.) to conduct phishing and malware campaigns.
We also know that hackers have been targeting organizations’ Remote Desktop Service (RDS) servers, knowing that these RDS servers are seeing dramatic increases in usage as people have shifted to remote work. So, the need to improve remote working security is there. Here are some tips that can help you. I’m going to focus on some practical steps you can take now, that don’t involve a major rollout to users (more on that later).
Patch, Patch, Patch
One of the most important steps you can take to improve remote working security (or any work security for that matter) is to keep your systems up to date with security patches. You may have to manage this after normal business hours. Regardless, keep your servers up to date!
Double Down on Phishing Education to Improve Remote Working Security
As you saw from the image above, hackers have not been slowed down by all the shelter-in-place actions. (Phone spammers… that’s another story.) With users working in a new context, it would be easy to let their guard down. For hackers, this is an even better time for those targeted spear-phishing attacks. The CFO isn’t in the office with the CEO, so maybe that request to wire funds seems more legitimate than it otherwise would be.
This is a good time to remind users about common phishing techniques and how to spot them. It would also be worthwhile to remind folks about processes (such as multiple approvals on wire transfers) that you have in place to prevent fraud. You might even run a phishing test, although I wouldn’t suggest you do that without warning folks that it’s coming.
Put Your Files in the Cloud
What does this have to do with improving remote working security? Getting user files in the cloud means you can steer them toward sharing links to files, vs. attachments to emails. If you’re already using some kind of protection against malicious links (e.g., Microsoft’s Advanced Threat Protection) then you can be more confident about users clicking on links in an email. The payoff? You’re reducing the possibility of organizational files being downloaded to a user’s home computer.
Enable MFA for Admin Accounts
I hope you’ve already done this. Since administrative accounts have more access to network resources, it’s especially important to harden their security. For heaven’s sake, move off the default password for the account. And consider making the username something hard to reproduce as well (shout out to Sean Frazier for that). Adding multi-factor authentication (MFA) to admin accounts will virtually guarantee that you’ve improved remote working security.
Restrict Hours of Access to Organizational Resources
Are your users all located in one time zone? Or spread across just a few time zones? You can improve remote working security by restricting the hours that RDS servers and other assets are available. Don’t leave the front door to the office unlocked if no one is there to provide security.
Pay Attention to Your Security Logs
We know we should be watching our security logs. We also know that alarm fatigue is real and we tend to ignore the logs. It’s more important now that you improve remote working security be spending time with security logs. Do you see access attempts from unusual locations? Are there brute-force attacks occurring on your RDS servers? Are users logging in from multiple locations at once? Be suspicious.
Spend a Little Time Thinking About How You’ll Prepare for the Next Pandemic
When you have a moment to pause and reflect, ask yourself: what things do you wish you would have done before, that would have made grappling with the sudden shift to remote working easier? What would you do next time to improve remote working security?
- I’d be thinking this is my “Y2K Moment” to convince the organization that we need to implement MFA. For everyone.
- This would be a great time to have some Conditional Access policies in place.
- Information Rights Management (IRM) is a project we tend to kick down the road. But having IRM in place would head off the spread of sensitive information beyond the bounds of your network.
Those are just a few items that come to mind. I’m sure you can think of several others.
One Day at a Time
One of the hardest things about this pandemic, for us cut-to-the-chase types, is that we can’t accelerate to the end. We have to take each day as it comes, watch the rates of infection, and look for signs that we’re flattening the curve. Maybe you wish you had done more to prepare. But don’t beat yourself up if that’s the case; we are where we are. Do congratulate yourself on getting things this far. Bravo! And be ready to come out of this asking what will be forever different and what will revert to the way it used to be. That’s what leaders do.





0 Comments
Trackbacks/Pingbacks