I think this is important, because risk assessment is intimidating. It’s not like buying some technology. Most IT managers aren’t trained to do it. It involves learning a specific analytical method, and then carrying it out with interviews, spreadsheets, and reading articles from standards bodies. Ecch!
So why do one? Basically, a risk assessment is for security what an IT assessment is for general IT strategic planning. It provides you with a plan for your future security efforts. Since security is such a changing, confusing field, this can be a great help.
Anybody can plan (well, almost anybody), but how do you know the plan is any good? How do you convince others, such as the people with the budget, to go along?
Remember the old days when the only people who would back up their computers were those who had experienced a hard disk crash? Security is a bit like that. Until you’re hit, you don’t appreciate how important it is. Once you’ve been hit, you’ll want a plan, unless you just outsource the whole thing.
So read our article when it comes out. You will be able to access it at https://www.tagtech.org/page/cybersecurity.
A Risk Assessment Checklist
By way of a preview of coming attractions, here is the article’s checklist of risk assessment tasks, from an early draft.
• Identify the assessment’s scope.
• Identify anything in your organization whose confidentiality, integrity or availability must be protected. Call these things “assets.”
• Identify the assets’ owners.
• Determine what could threaten each of those assets, what vulnerabilities each threat could exploit, and how your current security system is protecting them.
• Assign a value to each asset, based on what it would cost your organization if the asset’s confidentiality, integrity or availability were lost.
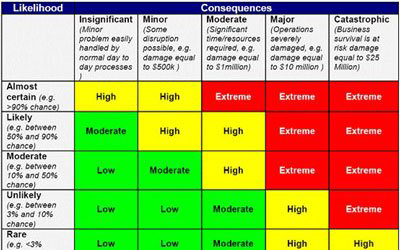
• Build and populate the risk assessment matrix.
• Determine acceptable and unacceptable risks.
• Propose ways to mitigate the unacceptable risks.
• Evaluate the ways to mitigate the unacceptable risks.
So read the article and do a risk assessment. After all, “No risk, no reward!”




0 Comments