But Does It Work? “Security Effectiveness Report 2020,” Mandiant Solutions, www.fireye.com, May 5, 2020
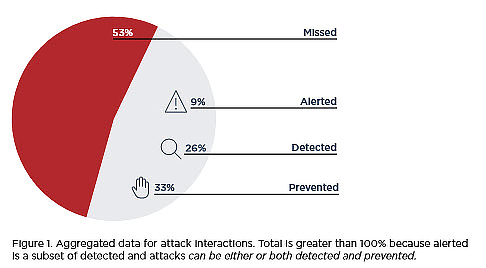
One paragraph in the report’s introduction says it all. “Our findings confirm the concern held by many security practitioners: Security controls are not performing as expected.” Most attacks go undetected, unprevented and without staff being alerted. Here are the percentages from the report:
The report offers both organizational and technical reasons for the situation. Definitely food for thought.
Teams Users Take Note: “Fake Microsoft Teams notification emails are hitting inboxes,” Zeljka Zorz, helpnetsecurity.com, May 4, 2020
A lot of our readers are Teams users, so we pass this along. Teams users are being targeted, and the emails are almost perfect forgeries. The fake login pages you go to are identical to legit Microsoft pages. As of May 1, Microsoft said 15,000 to 50,000 mailboxes had been attacked. If the attack succeeds, you give them your Teams credentials, and maybe a single sign-on.
WordPress Bad News: “A hacker group tried to hijack 900,000 WordPress sites over the last week,” Catalin Cimpanu for Zero Day, www.zdnet.com, May 5, 2020
Since April 28, according to cybersecurity firm Wordfence, nearly one million WordPress sites have been attacked by a single organization. WordPress website owners should update plugins and themes. They can also install a website application firewall (WAF).
WordPress Good News: “WordPress Releases Security Update,” U.S. Cybersecurity and Infrastructure Security Agency (CISA), www.us-cert.gov, April 30, 2020
The CISA recommends reviewing and updating to the latest upgrade, WordPress 5.4.1. Do it now. As the CISA said, “WordPress 5.4 and prior versions are affected by multiple vulnerabilities. An attacker could exploit some of these vulnerabilities to take control of an affected website.”
Those Inventive, Malicious People! “Upgraded Cerberus Spyware Spreads Rapidly via MDM,” Tara Seals, Threatpost.com, May 1, 2020
Researchers at Check Point found that 75% of the mobile users at a large multinational conglomerate were infected with an improved version of the Cerberus spyware. As the Check Point researchers said, “This is the first time we have a reported incident of lateral movement inside a corporate network that utilizes the MDM server as a means of spreading.” Apparently, it was a targeted attack. The Check Point report is here. Cerberus has also gotten more nasty, it now has a keylogger that can capture all credentials. It has special routines to capture Google Authenticator information, install TeamViewer, and much more.





0 Comments