My colleagues and I have written about various phishing techniques over the past couple of years, and the clues to look for in a message to determine if you are indeed being phished. Hopefully by now everyone at your organization has gotten some cybersecurity training and knows how to spot something “phishy”. (Well, they at least recognize the more basic attempts at phishing and social engineering.) And while the vast majority of phishing emails are still those typical typo-riddled ones sent from strange email addresses, or with their “enter your password to see what you’ve won!” blatant ploys, every now and then more sophisticated attacks emerge. Here are 3 new advanced phishing attack techniques, as identified by our partners, the cybersecurity pros at KnowBe4.
OAUTH Phishing
You know when you go to a new website and it asks if you want to log in with your existing Facebook, Twitter, Apple or Google account? Like this:
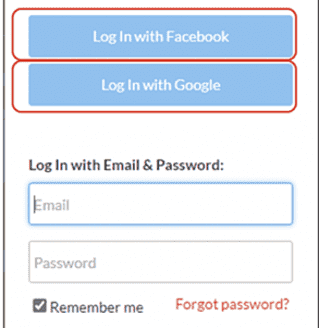
This is known as OAUTH, which stands for Open Authorization. It’s a relatively new but widespread standard allowing for one authenticated login for a user across various sites. Essentially, a single sign-on solution. Definitely convenient.
Well, hackers have caught on and are now exploiting OAUTH to gain access to all kinds of your personal information. Essentially, they’ll send a very normal, professional looking email, usually masquerading as an Office 365 message, with an attachment. When you click on the attachment, you then get an OAUTH prompt that requests permissions to access your information.
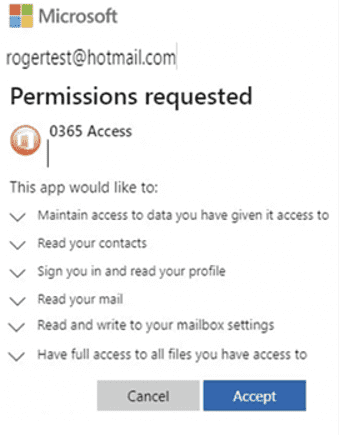
Still thinking this is a legitimate request from a legitimate sender you click “Accept.” (Perhaps not fully paying attention to what’s in that list of things to which you are granting access. Which, at least in the example above, is pretty much everything!) And unfortunately, “Accept” is also the default choice, making it even easier for you to make the wrong move. Now the bad guy can take over your mailbox, contacts, personal profile and more. Pretty scary stuff. You can read more about OAUTH phishing and what to look out for here.
Third-Party Phishing
Hopefully, we all know to be cautious with messages coming from people we don’t know. But hackers have a new tactic: After breaching an account (email, social media, etc.) – perhaps by using the OAUTH method I just told you about – they use THAT account to phish everyone in that victim’s contact list. After all, you typically wouldn’t think twice about opening and responding to a message from a friend or colleague, right? Well, now we have to be careful even with those. In fact, this advanced phishing technique has been tried out on me twice recently.
Phishing Attempt #1
A couple of months ago I got a fairly innocuous message on Instagram from a good friend. Or so I thought. After chatting briefly, “she” said something out of character about her kids and I started to grow suspicious. (OK, I’ll tell you because it’s funny: When I asked how her kids were doing, she said, “Oh, you know children! Growing like weeds!” Well, both of her kids, like mine, are in their mid-20’s. And not to mention that Patty never uses cutesy expressions like “growing like weeds”.)
Now that my phishing radar was in going off, I continued to play along, just to see where this was going. Sure enough, my “friend” asked if I had claimed my pandemic stimulus money yet (for which neither of us – me nor my real friend — were eligible. Never mind that there was no “claiming” involved in receiving that money). And then came the expected zinger: “I got my money already! You just need to go to this website <www….etc> to claim your money and they send it right away!” At that point I told the person the jig was up (you know, like a detective in an old-timey movie) and then texted my REAL friend via SMS to tell her someone had compromised her Instagram account.
Phishing Attempt #2
Ironically, just this morning I got this via Facebook Messenger from an old high school classmate I don’t think I’ve ever conversed with via private messaging:
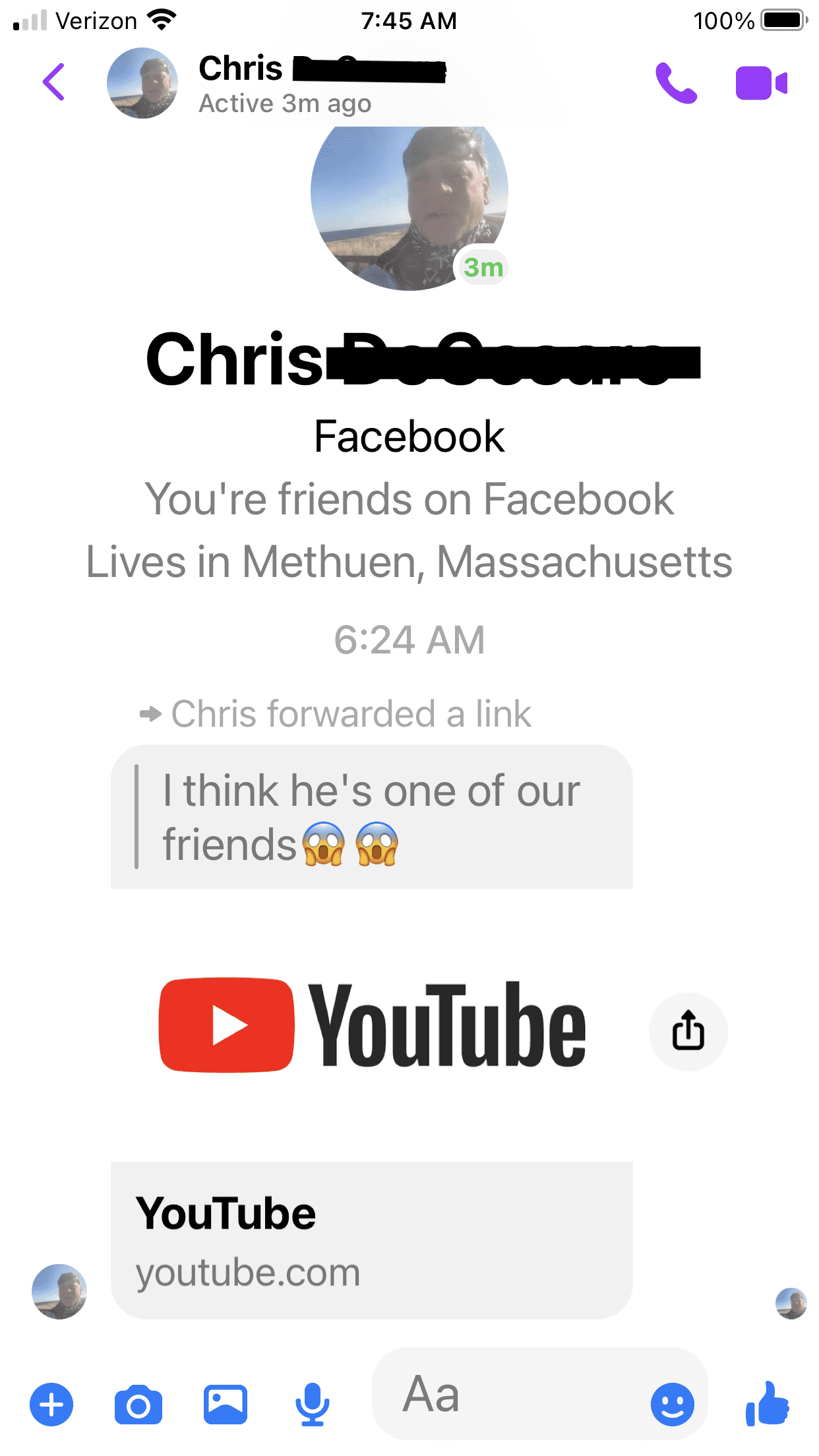
I’m sure that if I clicked on the YouTube video I would have either downloaded malware, or perhaps gotten that OAUTH prompt to log in. (A note: I’ve gotten messages similar to this in the past and a common theme is that they used the “shocked” emojis. I suppose to make the alleged video even more intriguing to the victim. Because after all, who among us can resist taking a peek at a good train wreck?)
The bottom line is this: Now not only do you need to be wary of messages from addresses or social media accounts you don’t know, but also even from those you do. If anything in a message sets off that little “something seems not quite right” alarm, trust your gut and proceed with caution!
Personalized SMS Messages
Phishing messages coming to you via text is nothing new. But in the past, they have been pretty generic and easy to pick out as annoying spam at the very least, or as an attempt to gain access to personal information at the worst. However, as hackers get more savvy, and more advanced phishing email techniques emerge, these messages are becoming personalized.
Thanks to the Internet and the dark web, most of our names and associated cell phone numbers are out there. So SMS phishers are taking the time to make their text-based phishing (also known as “smishing”) more believable, by inserting the victim’s name, email address, or other personal information into the text message. Here are some examples:
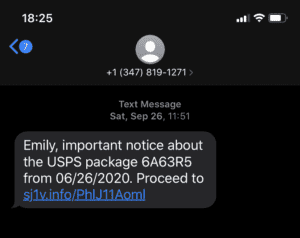
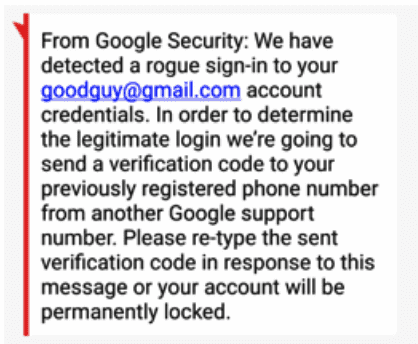
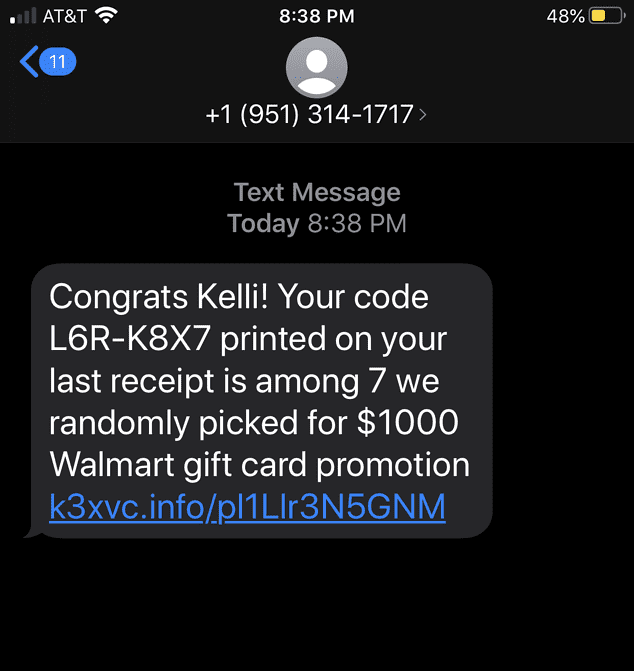
You are far more likely to click on a link in a message that appears to be from a recognized business or institution if the message mentions you by name. (See my post from last fall about the smishing scam that impersonated the USPS.) That’s when remembering some of the tell-tale signs of a smishing message come in handy:
- The text has a sense of urgency to it.
- A link in the text appears to be legitimate but takes you to a website whose URL doesn’t match the address of the company’s website.
- The text looks significantly different from other texts you’ve received from that company.
- The message requests personal information, like a credit card number or account password (obviously this is always the biggest red flag!)
In essence, if you get a text message that is unsolicited, unexpected and contains an attachment – regardless of whether or not the sender is addressing you by name — be cautious with how you proceed.




0 Comments