I was conducting some security training last week, where I focused on how to spot phishing messages. Maybe that meant that I had my phishing “radar” on high. Whatever, the reason, I was a bit surprised when I received two different messages that were easy to spot as phishing attempts. Take a look:
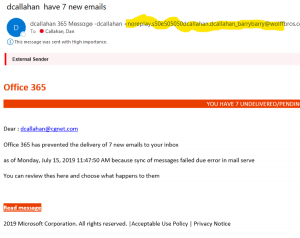 I was happy to see that this phishing message illustrated several of the “tells” that I had highlighted in my security training. Let’s go through them.
I was happy to see that this phishing message illustrated several of the “tells” that I had highlighted in my security training. Let’s go through them.
Bad Email Domain is a Giveaway
Look at the sender’s email domain (that part I clumsily highlighted). If this was a legitimate message, I would have expected to see something that included Microsoft.com. This is clearly not that! Even the Display Name (“dcallahan 365 Message – dcallahan”) is not what you’d expect from a legitimate Microsoft support person.
Some Social Engineering
One of the points I made during my recent security training was that phishing messages appeal to your emotions in order to encourage you to click or respond. (More in this article by the folks at BeenVerified. [Link updated on 10/05/2020.]) In this case, see the banner headline (it’s cut off in the image) that says YOU HAVE 7 UNDELIVERED/PENDING MESSAGES. Why would someone put this in a phishing message? It has a couple of emotional triggers.
- Curiosity. I kind of want to know what those messages are. After all, they could be important!
- Fear. In this case, the phishing message tries to generate a fear or losing out. Put another way, it attempts to use scarcity to make responding into a compelling event. If I don’t do something soon, these messages are going to go away forever!
Did you notice one other bit of social engineering? That’s right; look at the footer of the email. It sure looks like it comes from Microsoft. (They would have gotten bonus hacker points if the Privacy Notice and Acceptable Use Policy were links back to the phishing site.)
And yes, there it is. The Read message button that will take me to the phishing site.
Spelling and Grammar Mistakes are Another Clue
I teach that it’s reasonable to presume that any legitimate business email will be largely free of grammatical and spelling errors. Look at the errors in this message.
- There’s no © in front of the 2019 Microsoft Corporation.
- The email domain likely has a spelling error: “noreplay” instead of “noreply”.
- “mail serve” should be “mail server”.
- “thes” should be “these”
- None of the sentences ends with a period.
Calling dcallahan
The last clue in this message is an interesting one. My email address starts with d.callahan, not dcallahan. The phishing folks must have known this, since they used my correct email address to send me this phishing message. And yet, they address the message to dcallahan@cgnet.com instead of d.callahan.
Second Phishing Message. Same Sender?

Look at this phishing message. I received two of these on the same day. The Display Name what I might expect from a legitimate support message. And I like their box at the bottom of the phishing message, informing me that “This email is from a trusted source”.
On the other hand, look at the Office graphic. It’s been distorted. That was the first thing I noticed, and it immediately made my suspect the message. This phishing message also refers to me as dcallahan@cgnet.com. This makes me wonder if the same sender sent both of these phishing messages.
Receiving these messages was a good reminder that we can all use a refresher course in common phishing techniques!




0 Comments
Trackbacks/Pingbacks