Looking at Azure AD Sign Ins…
We know that one security area to watch is Azure Active Directory (AAD) sign in attempts. Attackers commonly use hacked user credentials to gain entry to an organization’s network. So, it would be nice to know what’s going on in this area. Here are some screenshots from the AAD Sign In dashboard.
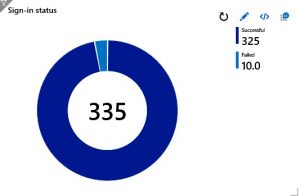
As you can see, CGNET’s Azure Sentinel data has logged a little over 300 AAD sign ins over the last 24 hours. We have staff all over the world, so seeing sign ins at all hours is not so unusual for us.
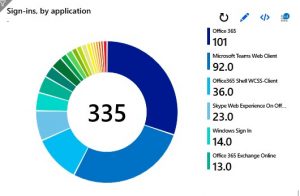
That number is also high because some sign ins occur via opening an associated application, as you can see here.
 It’s also nice to review Azure Sentinel data to see where the sign ins are coming from.
It’s also nice to review Azure Sentinel data to see where the sign ins are coming from.
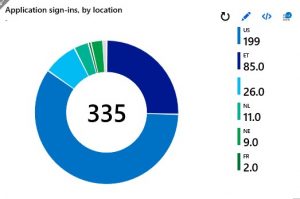
In our case, you can see that our people in Ethiopia have been busy signing into Azure AD.
… and Azure AD Sign In Failures
Where things get interesting in examining Azure Sentinel data is the area of failed sign-ins. It’s easy to track failed sign in attempts by user, IP address and location. Here’s a chart of failed sign ins by location.

And here’s a table with more detail on failed sign ins. Here we can see information on what user failed to sign in, what IP address the sign in attempt came from, and the reason for the failure.
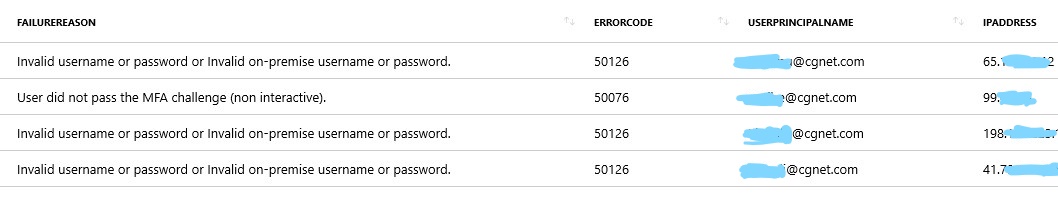
We may want to confirm that the failed sign in attempt from Saint Kitts and Nevis is from a CGNET domain user.
Beyond security concerns, the Azure Sentinel data can also tell us if specific people are having repeated sign in failures and why. We could use this information to target some remediation or training for this user.
Where to With Your Azure Sentinel Data?
This post just scratches the surface regarding possible log data to connect and examine. We’ll be looking at other interesting services down the road. Stay tuned! If you try Azure Sentinel out be sure to let me know about your experience.
Stepping back from the data, it’s amazing to consider what Azure Sentinel represents: a DIY SIEM. You can add data connectors little by little, tuning the service to deliver just the information that would be useful in your security efforts. The dashboards are great out of the Azure Sentinel box, and they can easily be modified, filtered, embedded and extended.





0 Comments