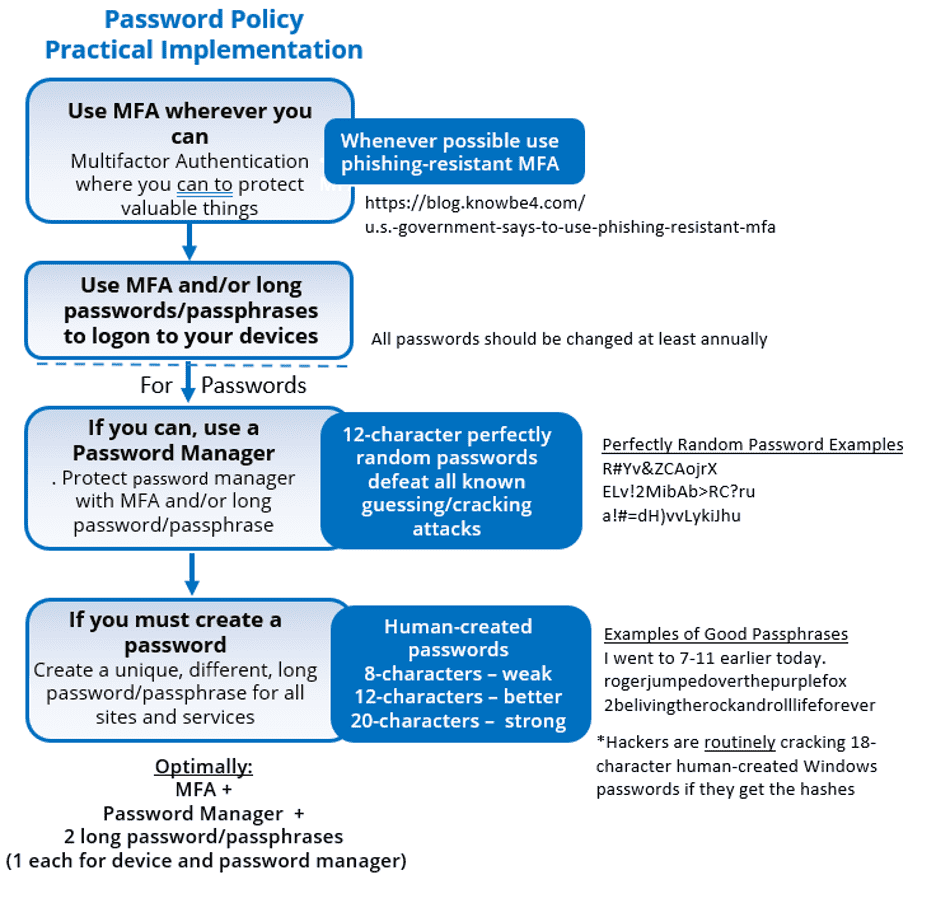
After several months of research, our partners at the cybersecurity firm KnowBe4 released their official recommendations regarding the ideal password policy. They put out a free 41 page e-book with the detailed guidance, but in this post I will summarize and discuss their recommendations. I’m also including their helpful infographic.
Top password policy recommendations
Here are the bullet points from their recommendations:
- Use phishing-resistant multifactor authentication (MFA) wherever you can
- If you cannot use MFA, then use an automated password manager to create long, complex random passwords
- If you MUST create your own passwords, make them 20-characters or longer
According to KnowBe4, the ideal scenario is where everyone has only one or two human-created long passphrases and then uses MFA and/or a password manager for everything else. You would need the long human-created passphrases/pass sentences only to log into your device(s) and your password manager (if not using MFA).
NIST’s unexpected guidance
The official password policy guidance released in 2017 by the National Institute of Standards and Technology (NIST) surprised everyone by saying that long, complex passwords were NOT necessary. Also, that changing passwords regularly was unneeded. Their reasoning was that when it comes to most attacks against passwords, it simply doesn’t matter what your password is. Why? Because hackers can get them through social engineering (simply tricking someone into giving up their password) and via malware attacks. Neither method is thwarted by the length or complexity of the password. They also believe that when users are forced to create long, complicated passwords, they are far more likely to reuse them across multiple websites and services, providing further risk. NIST’s advice – which went against all previous recommendations – was so divisive that to this day most regulatory guides still do not allow short, non-complex and never-changing passwords.
The one thing they both agree on
According to KnowBe4, NIST is right about one thing: People who have to create long and complex passwords will likely want to reuse them across multiple unrelated sites and services. It is preferable not to require them to do that for the majority of their online activity. This is why they recommend primarily using MFA, secondarily, a password manager that generates lengthy, random passwords, and finally, just that one (or two) VERY long – 20 characters at minimum – passphrases or sentences only to access devices and the password manager.
Proof that length and complexity do matter
There are two attack scenarios where the length and complexity of a password are important: password guessing and password hash cracking. The rate at which an attacker can guess at a particular password in an online attack is limited by the how many guesses the attacker can make in a particular time period. While many systems limit guessing to a handful of guesses before locking the person out (we’ve likely all had this happen at some point!), there are scenarios where attackers have had an unrestricted ability to guess (using software) at a speed approaching over 100,000 times a day. Nonetheless, it has been shown that a 12 (or more) character, random and complex password (such as those created by password managers) are almost impossible to crack. Either through password guessing or password hash cracking mechanisms (which can guess at many trillions of guesses a second), the random 12+ character password is virtually unguessable.
A far greater risk
The main reason that the KnowBe4 pros disagree with NIST’s relaxed password recommendations is that password hash cracking has recently become a much bigger threat. It may be true that password theft (via social engineering or malware) comprise a far greater percentage of attacks right now, and with those attacks, your password length and complexity do not matter. However, it is also true that password hash cracking has become easier to do than ever before (particularly on Windows devices and networks) and can result in a far greater overall security risk to organizations. If an attacker can gain access to your network, those shorter, human-created passwords can be compromised in no time at all. This has been proven by the work of actual hackers as well as cybersecurity professionals running penetration testing every day.
Until we move beyond passwords…
According to KnowBe4, NIST is generally dismissive of passwords (and PINs) completely, regardless of entropy and make-up, except for the lowest value systems. It is clear that NIST wants everyone to move away from password-based authentication altogether because of all the threats and attacks against them. But while we are getting close, we are not all the way there just yet. This means that 12+ character randomly generated passwords or 20-character or longer human-created passphrases are essential. And because no one wants to have to create and remember a bunch of really long passwords, follow their password policy advice and use phishing-resistant MFA and password managers whenever you can.




0 Comments