It is raining again here in Northern California (but we are not complaining!). And in the technology world, it...
Search Results
Unmanaged IT Assets: What You Don’t Know CAN Hurt You
When was the last time you took a look at all of your IT assets? And I mean, ALL of them? There are several reasons...
Separate Your Regular and Administrative Accounts
I had a call today to answer questions about a security audit we recently finished. The customer had several questions...
You Can Help a Smaller Organization Be CyberSmart
I have been on a mission for a while now, looking for ways to push cybersecurity knowledge out to smaller...
What You Should Do About the LastPass Breach
Welcome to 2023! What with the holidays (you do remember them, right?) and the end-of-year distractions (hello, bomb...
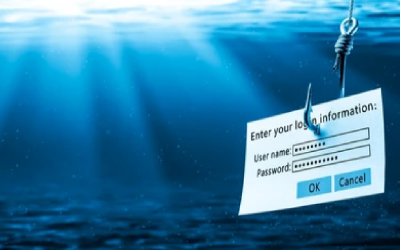
Top Phishing Trends in 2022
Our partners at cybersecurity firm INKY just came out with their “Email Security Annual Report” for 2022-2023, chock...
Clone Phishing: A Scary New Tactic
Oh boy. These guys just don’t stop; they’re coming up with new tricks to steal our data, left, right and center. The...
The Online Holiday Scams You Need to Look Out For
Yes, my friends, it’s that time of year again. Time to start making our lists and checking them twice. Time to start...
Match the Scale of the IT Provider to the Size of Your Nonprofit Budget
I recently wrote about the challenge facing foundations who want to fund IT and cybersecurity work in the nonprofits...
Can We Please Stop Making it So Easy for the Hackers?
Ahhh, passwords. The bane of our collective existence. Yes, we know we need them to protect our private information....
Phishing in Your Own Pond: The Importance of Simulated Phish Tests
Phishing simulations are a key part of any comprehensive security awareness training program. By sending out fake...
We Are Here for You with Zero Trust Resources
Zero ____. It is one of this week’s New York Times crossword clues. (Don’t tell me the answer. I have not solved the...
Four Factors for Effective Security Awareness Training
Social engineering remains the top way criminals infiltrate an organization’s data, and the problem gets worse every...
Yes, MFA Can Be Hacked. Now What?
I read a blog post today from our friends and partners at cybersecurity firm KnowBe4 that was a bit unnerving. While...
Do Your Security Actions Make Sense?
Do your cybersecurity actions make sense? Wait, what? Sometimes we cybersecurity folks can get carried away. More...
Let ComplyUp Take Care of Your Security Compliance Planning
I have written in the past about using a tool to assess your organization’s compliance against a security standard....
How Secure are Password Managers?
We’ve recommended using password managers many times in past posts. (See here and here). But the usual worry still...
Trending Cyber Threats Spell No Summer Vacation for You
I want to talk about trending cyber threats. What they are, and why it means there will be no summer vacation for you....