Hacking is a thriving business. We hear about it in the news all the time these days. When we think of a hacker, we imagine a computer whiz who has the technical expertise to “break in” to computer systems. The high school nerd who works his way into the school’s admin computer to change grades. The tech genius who has the know-how to hack into government systems to wreak havoc or steal data.
But there is another type of hacker who uses an entirely different set of skills to get the information they want. They are the social engineers: hackers who exploit aspects of human psychology to ensnare their victims and trick them into getting what they want.
Social engineering utilizes a broad spectrum of methods – none of which are mutually exclusive. I’m going to help you get familiar with some of the most common tactics. That way you can be on the lookout for yourself and also help educate other members of your organization.
Phishing
You’ve likely heard the term “phishing” by now; this is the most common type of social engineering attack. The bad actor uses email, social media, instant messaging, texting or phone calls to trick their victims. The goal: Getting them to give up up private information or visit a malicious website that will compromise their system.
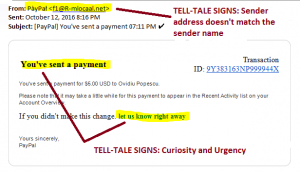
These social engineers are very good at replicating messages from official-looking sources. They can spoof logos, images and texts to look nearly identical to a legitimate source. However, there are some telling signs you can look for.
Phishing tip-off #1: Urgency
Any message expressing urgency of action – particularly an action that requires providing private or financial information — should be questioned. The hacker is playing to your fears: X has happened and you should do Y immediately to correct the problem (see Example 1). Or, more subtly, they ask you to confirm something they say you’ve already done, even something minor (see Example 2). (You know, of course, that you haven’t. But human nature motivates you to respond to correct the mistake quickly.) When you see messages like either of these, take a moment to stop and read them again. Slowly and carefully.
Phishing tip-off #2: Mismatched addresses
Check the sender’s address as well as link addresses within the message. If not from a legitimate source, you may discover the “from” address is not what it initially appeared to be. (For example, a number “1” is substituted for a lower-case letter “L”.) Or there is some other hard-to-notice-at-a-glance minor spelling error, like an extra letter. In less sophisticated cases, hackers don’t even bother to mimic a legitimate address; they just assume you won’t notice.
Also inspect any links within the body of the message they are trying to get you to click on, to reply to. If it is completely different from the sender’s in the “From:” line, be wary. Even trickier: the URL you are to click on looks the same as the sender’s “From:” address. But in fact, it is hyperlinked to a different destination altogether. (If you hover your cursor over the link the true URL will appear.) Bottom line: Do NOT reply or click on anything until you’ve thoroughly inspected any and all addresses in the message!
Example 1:

Example 2:
We have written quite a bit about phishing before. For more details on how so spot a phishing message, read Dan Callahan’s “Anatomy of a Phishing Message”. Also check out Tim Haight’s Phishing in Your Users’ Pockets for a post specifically about phishing via mobile phones. And I wrote a kind-of Phishing 101 post about a year ago that might be helpful: Phishing Scams: Don’t Be Lured In! Finally, be sure to read Dan Callahan’s post from today that walks you through the specifics of an attack that just happened to one of our customers.
But while phishing in its various forms is the most common form of social engineering, there are others to look out for.
Pretexting
Pretexting is a form of social engineering where the hacker maintains a fake persona to trick their victim. Unlike phishing, which plays off fear and urgency, pretexting works from a false sense of trust to extract information. In essence, setting the “pretext” of a trustworthy relationship between scammer and victim.
A scenario using the pretext technique might go something like this:
The scammer has already – via phishing or by some other means – gathered enough personal information on a member of an organization to create the pretext of being a person of some authority within that company. He or she then calls the IT Help Desk pretending to be that person with a made-up problem. Already armed with personal information and therefore appearing trustworthy, he requests further personal information needed to resolve the phony problem.
The difficulty in protecting your employees from this type of scam depends on the size of your organization. If you are a smaller company, it’s pretty easy to know if someone who says they work for your company actually does. But this is much more difficult if you have a large organization. In that case, unfortunately, the best bet is to trust no one! Have staff request employee ID numbers when requests are made, and then separately vet the person before providing any further help.
But no matter the size of your organization, if a person claims to be from *outside* the organization but with permission and/or authority to gather data, instruct your employees to be proactive in checking out their identity. (Again, trust no one.) Get the person’s name, company name, phone number, etc., and use every tool at your disposal to verify, verify, verify!
Baiting
Baiting is in many ways similar to phishing. However, this form of social engineering is counting on a person’s natural curiosity and desire to get something for free. Baiters may offer users free music or movie downloads, if they give them their login credentials to a certain site. (Of course, the only free thing they will get is a world of headaches!)
Some baits rely only on the element of human curiosity. The perfect example of how little it takes to trigger this natural reaction and potentially bring great harm to an organization was demonstrated back in 2006. A network security firm hired by a credit union to assess their network came up with a simple, clever way to bait employees into unwittingly giving them private data from their computers. They scattered 20 USB drives – set up with a Trojan virus to collect passwords and other information — throughout various areas of the facility frequented by employees (parking lot, smoking areas, etc.). They then stood back and watched as every single USB drive that was picked up (15 in all were found) was brought inside and popped into employee’s desktop machines! As the employees scrolled through the images planted on the drives, they did not know they were simultaneously sending all sorts of private data to (fortunately, in this case) the security team. You can read the article published back in 2006 here.
Quid Pro Quo
Although a lot like baiting, quid pro quo attacks are more transactional (as the name implies: I’ll do something for you if you do something for me.) Generally, the hacker is offering a service in exchange for an action that will supposedly make it possible. A common example is the hacker impersonating an IT staffer within a large organization (see pretexting above). They call up an employee (well, perhaps several employees until one takes the bait) claiming that they need their help in order to administer a software upgrade for their team that some “higher up” requested for their team. They request the employee to do something to make that possible (supply some password or turn off a firewall). The employee believes they are doing something to help the IT staffer fulfill his obligations AND are getting something in return. In fact, they are allowing the bad guy in to do something altogether different (install not an upgrade, but malware).
Tips to avoid becoming a social engineering victim
- Consider the source – and then check it out. If little red flags went up while you were reading a message (based on some of what you read above, or just your genuine, human intuition), click on nothing. Leave email (or the text, if on your phone), and use your browser to check out URLs, or just go directly to the main website of organization supposedly seeking your input and proceed from there.
- Slow down. Re-read. Look for errors in spelling, wording or anything else that seems ”off”.
- If it sounds too good to be true – or in some cases, too strange to be true – it probably is. Investigate and verify. (See: Nigerian prince email scam, which has been around for a long time. Yet from what I just read here, continues to rake in big bucks to this day!)
- And it should go without saying: Make sure you have antivirus software or a security suite installed, and that it is up to date on all of your devices!





0 Comments